25 Reasons Apyx Is Built to Be Trusted

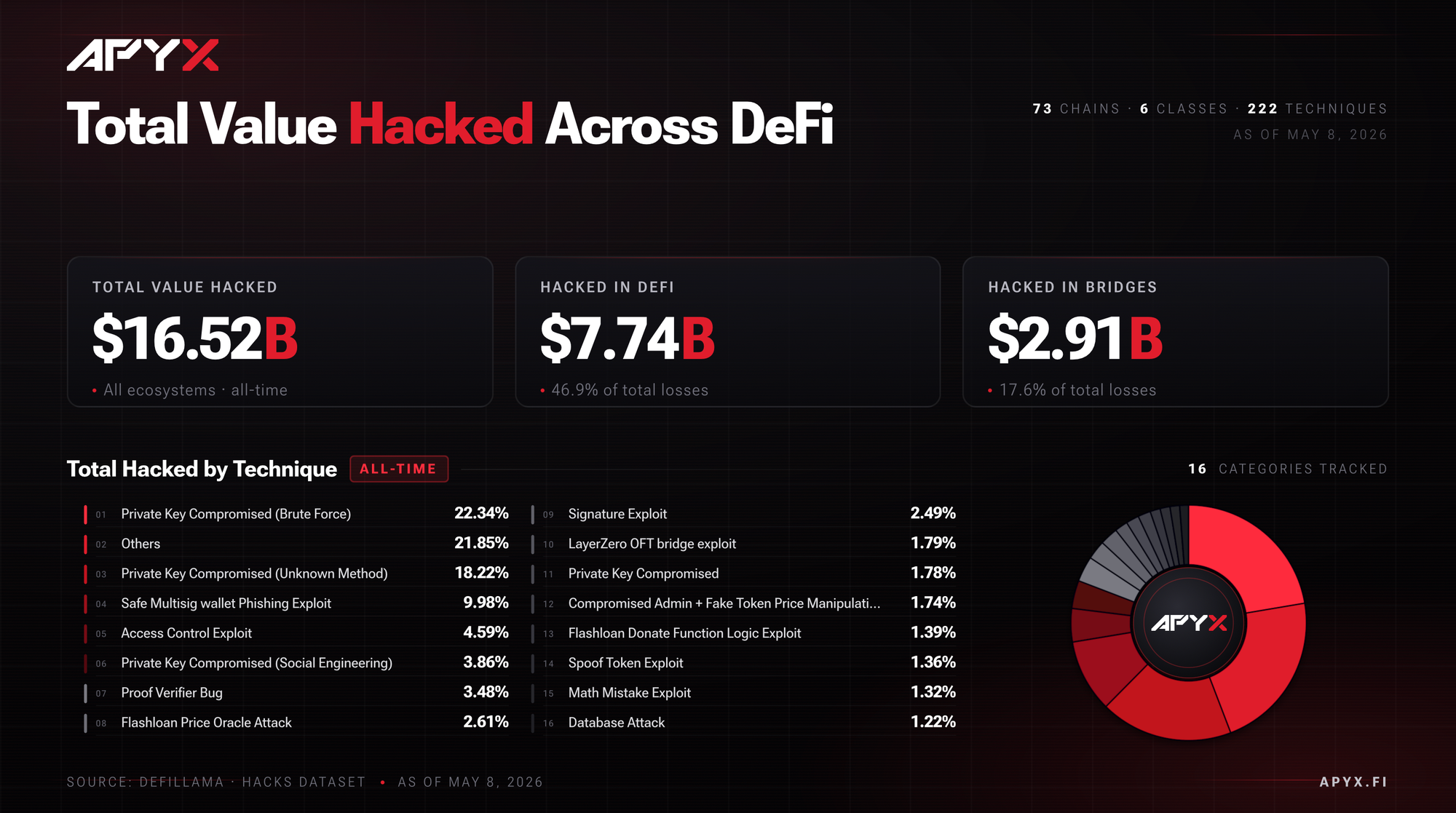
The past several months have been demoralizing for DeFi. From the $292M Kelp DAO bridge exploit in April, to the $285M Drift Protocol breach also in April, and the $80M Resolv Labs minting attack in March, nearly $770M has been lost to exploits across major protocols so far in 2026. The pattern across these incidents has been telling and has made market participants question the return they're generating relative to risk.
The damage is no longer concentrated in smart contract bugs. It now spreads across bridge misconfigurations, compromised signing keys, unbounded minting paths, infrastructure failures that sit outside the onchain code entirely, and in more cases than people know, lazy operational security.
At Apyx, security is not treated merely as a feature, it's foundational to our current and future success. Every decision about how the protocol is secured, from who can execute a mint to who can upgrade a contract, was made with the assumption that any single point of control would eventually be tested. The result is a layered architecture designed to remain secure even under adversarial conditions.
Given recent events and lingering fears, we want to give current and prospective users a clear view into the specific controls protecting their money on Apyx. What follows is a concise breakdown of what we are doing today, and why our users can sleep well at night.
Audits and External Review
The first line of defense is rigorous, independent review of the code itself. Apyx has commissioned multiple audits across multiple firms with overlapping but distinct methodologies, so that no single auditor's blind spot becomes the protocol's blind spot.
1. A dedicated Quantstamp audit of our Chainlink-powered cross-chain bridge. Bridges have been the single largest source of value lost in DeFi over the past several years, accounting for roughly 40% of all hacks since 2022. Recognizing that, we commissioned a separate, dedicated audit of the bridge infrastructure used to move apxUSD and apyUSD across chains. The full report is available here.
2. Three additional independent audits have already been completed on apxUSD. Quantstamp, Certora, and Zellic each conducted a full review of the apxUSD codebase. Three firms reviewing the same code means three independent threat models, three different review methodologies, and three different sets of expertise applied to the same problem.
3. Zellic was founded by the top-ranked competitive hacking team globally in 2020, 2021, and 2023. Capture the Flag competitions are how the security industry tests its best offensive researchers. The engineers behind Zellic spent years winning those competitions before turning their expertise toward auditing protocols. When they review code, they do so with the mindset of an attacker.
4. Certora has also been engaged to review our multi-sig setup and threat model. Smart contract audits are necessary but not sufficient. The systems that govern who can take what actions, and under what conditions, are equally important to get right. Apyx is treating governance security with the same rigor as smart contract security, and any major future changes to the admin setup will also be reviewed by a third party.
5. Reserves are published in real time by Accountable, with cryptographic proofs of solvency. Periodic attestations are no longer enough. The Resolv exploit exposed eighty million dollars in unbacked tokens that existed for hours before anyone could verify the discrepancy, and that gap between issuance and verification is exactly where the worst stablecoin failures live. Apyx publishes its reserves continuously through Accountable, a proof-of-reserves system that runs inside a secure enclave and produces cryptographic proofs of solvency that anyone can verify. The enclave architecture means the reserve data cannot be modified without the modification being cryptographically obvious. Users do not have to trust a press release or wait for a quarterly attestation; they can verify the backing themselves, at any moment.
Access Control and Governance Architecture
Beyond the code itself sits the question of who can take what actions. A protocol with flawless contracts can still be compromised if administrative control is concentrated in too few hands or moves too quickly. Apyx is built around the assumption that any single point of control will eventually be targeted, and the governance architecture is designed accordingly.
6. Every sensitive function is gated by a single OpenZeppelin AccessManager contract. This means there are no backdoors, no hidden admin keys, and no implicit permissions anywhere in the protocol. Nothing happens without being explicitly permitted by this contract, which is itself a battle-tested standard maintained by one of the most respected security teams in the space.
7. Admin actions require a 4-of-6 multi-signature approval, expanding to 5-of-7 as the protocol grows. A multi-sig is exactly what it sounds like. Multiple separate signers must independently approve an action before it can take effect. Even if one signing key is lost or compromised, that key alone cannot do anything consequential.
8. Day-to-day operations require a separate 3-of-6 multi-sig, split across five tiers of execution delays. Operational tasks need to move faster than administrative changes, but they still require coordination. The tiered structure means the time required for an action to take effect scales with the impact of that action. Pausing a contract in an emergency happens quickly. Larger changes sit in a queue.
9. Signers are distributed across three countries and three different firms, with dedicated signing devices separate from their daily drivers. Geographic and organizational distribution makes coordinated compromise materially harder. An attacker cannot simply target one office, one jurisdiction, or one company to gain enough signing authority to move funds. Each signer also maintains hardware reserved exclusively for transaction signing, so even a fully compromised personal laptop cannot produce a valid signature.
10. Contract upgrades require a mandatory 7-day onchain delay. Any change to the underlying code of the protocol must sit visibly onchain for a full week before it can take effect. That window gives token holders, auditors, and the broader community time to observe what is queued, ask questions, and respond if something looks wrong.
11. Granting a new operator role requires a 3-day waiting period. Adding a new signer to the system is one of the most sensitive actions possible, because it expands the set of people who can take action on the protocol's behalf. We require three full days of public visibility before any new role activates.
12. Delays cannot be bypassed, even by the admin multi-sig itself, without triggering their own waiting period that is also visible onchain. This is the kind of detail that matters most when something goes wrong. There is no shortcut, no override switch, and no emergency lever that lets administrators move faster than the timelocks allow. The delays are absolute.
13. Every pending governance action is publicly visible onchain from the moment it is scheduled. Anyone, including external monitoring services, auditors, and the community, can see exactly what is queued, when it will execute, and what it will do. Nothing significant can happen quietly.
14. Any single signer across both multi-sigs can veto a pending action. The effective threshold for cancellation is one of six. A single on-call team member who notices something suspicious can single-handedly stop a scheduled operation without needing to coordinate with anyone else. An attacker who manages to get a quorum still has to outrun every guardian.
Minting Controls
Minting is the most sensitive control surface in any stablecoin protocol. The Resolv exploit earlier this year showed exactly why; an attacker compromised cloud infrastructure and minted eighty million USR tokens with no backing, causing the stablecoin to depeg by 47% and triggering bad debt across multiple lending markets. Apyx is built so that even a worst-case compromise cannot produce that outcome.
15. Minting is manual and multi-step, with no automated minting path and no single-transaction mint. There is no script, no API call, and no cloud service that can produce apxUSD on its own. Every mint requires deliberate action by authorized humans through a defined approval workflow.
16. Every mint request triggers a PagerDuty alert that an on-call operator must acknowledge before execution. The moment a mint is requested, an alert fires to a human being on call. That person reviews the request to confirm it is expected, correctly sized, and consistent with normal operations. The alert escalates automatically if it is not acknowledged.
17. A mandatory 4-hour window between mint request and execution enforces human review on every single mint. The window cannot be skipped. It exists specifically so that there is always time for a human to review and, if necessary, cancel a mint before it completes.
18. Three overlapping mint limits are enforced onchain. A maximum per-mint amount, a total supply cap, and a rolling 24-hour issuance ceiling all apply simultaneously. These limits operate regardless of authorization, which means that even if every other control somehow failed, the size of any unauthorized issuance would still be hard-capped at the contract level.
19. Changes to mint rate limits require a 3-day delay and can be cancelled by any single signer. The mint rate limit is the hardest cap on blast radius in the entire system. Even if every other control somehow failed, the rate limit alone would bound the size of any unauthorized issuance. Recognizing how critical that control is, Apyx requires a mandatory 3-day onchain delay before any change to the rate limit can take effect, and any single signer across the multi-sigs can cancel a proposed change during that window. The control that protects users most is the control that is hardest to weaken.
Operational Security
The largest losses in DeFi this year have not come from smart contract bugs. They have come from compromised devices, social engineering, stolen private keys, and pure laziness. The defense against these threats is not onchain. It is in the operational discipline of how the team handles its keys and monitors its systems.
20. Every signing key lives on a dedicated hardware wallet. Signers do not approve transactions on the same computers they use for everyday work. All signing activity takes place on separate, dedicated devices reserved exclusively for that purpose. This eliminates an entire class of risks that have compromised other protocols, including browser-based attacks, malicious software, clipboard hijacking, and social engineering targeting daily-use devices.
21. 24/7 PagerDuty coverage runs on every multi-sig action and every AccessManager call, with automatic escalation if alerts are not acknowledged. Onchain delays only matter if someone is watching during the delay. We have integrated PagerDuty across every critical control surface so that the protocol is monitored around the clock, not on a best-effort basis.
22. Guardians are also on PagerDuty and get notified the moment a transaction is submitted. The people who hold the cancellation authority described in point fourteen are the same people who receive real-time alerts. Every link in the response chain is staffed and monitored continuously.
Cross-Chain Infrastructure and Team
The final layer is the infrastructure Apyx relies on to operate across multiple chains, and the experience of the team behind the protocol.
23. Cross-chain expansion runs on Chainlink CCIP, with hard daily limits capping bridge exposure at 2% of TVL. Chainlink CCIP is the most battle-tested cross-chain messaging infrastructure in production. When the Kelp DAO bridge was exploited for nearly three hundred million dollars in April, the failure traced back to a misconfiguration in a "modular" bridge setup where the protocol team had to make their own security decisions. CCIP works differently. It provides a fixed security model that does not require each integrator to reinvent verification from scratch. We chose it specifically because it removes a category of risk that has cost the industry billions. As a second layer of protection, Apyx also enforces strict daily bridging limits: $5M/day for apxUSD and $2M/day for apyUSD in either direction. That caps total daily bridge throughput at $7M, roughly 2% of TVL, so even a worst-case bridge compromise cannot drain more than a small fraction of protocol value in any 24-hour window.
24. Chainlink Data Feeds power price oracles across the protocol. Oracles are how a smart contract knows what an asset is worth. Bad oracle data has caused some of the most significant exploits in DeFi history, often through manipulation of low-liquidity price sources or single-source feeds. Chainlink's decentralized oracle network is the industry standard precisely because it is hardened against those failure modes.
25. The core team has been in crypto since 2013, with decades of collective operational experience at Kraken. From Mt. Gox to the 10/10 liquidation event, the team has lived through every major industry stress event in crypto history. That kind of operational scar tissue is impossible to replicate. It informs every architectural decision in this list and every decision still to come.
Maintaining Trust
Security in DeFi is not a static achievement, it is an ongoing discipline that requires constant attention. The controls described here represent the current state of the Apyx protocol, but the work is far from over. So long as Apyx has users, we will continue expanding the audit footprint, hardening the operational stack, and tightening the governance architecture as the protocol grows.
The principles behind that work will not change: no unilateral control, no hidden actions, no single points of failure, and no unbounded blast radius. Trust in a protocol must be earned and maintained through verifiable controls, not through reputation alone, and we intend to keep earning it.